Blog
Connected battery storage systems face multiple cybersecurity risks due to their digital connectivity, IoT components, and network integration points. These vulnerabilities include unauthorised access, malware infections, data breaches, and system manipulation that can disrupt operations, compromise sensitive information, and threaten grid stability. Understanding these risks and implementing proper security measures helps protect your energy infrastructure from cyber threats.
What makes connected battery storage systems vulnerable to cyber attacks?
Modern battery storage systems create numerous attack vectors through their interconnected digital infrastructure and remote monitoring capabilities. These systems rely heavily on IoT devices, communication protocols, and network connectivity that cybercriminals can exploit to gain unauthorised access.
The digitisation of battery management systems introduces several vulnerability points. Smart inverters, monitoring sensors, and control systems all communicate through various protocols including Modbus, DNP3, and Ethernet-based networks. Each connection point represents a potential entry for malicious actors seeking to infiltrate your energy infrastructure.
Remote monitoring capabilities, while beneficial for operational efficiency, expand the attack surface significantly. Cloud-based dashboards, mobile applications, and web interfaces provide convenient access to system data but also create pathways for cybercriminals. The integration with smart grid systems further increases exposure, as these connections link your battery storage to broader energy networks.
Legacy systems pose additional risks when retrofitted with modern connectivity features. Older battery management systems weren’t designed with cybersecurity in mind, making them particularly vulnerable when connected to modern networks. The combination of outdated security protocols with new digital interfaces creates significant security gaps.
What are the most common cybersecurity threats targeting energy storage systems?
Malware infections represent the most prevalent threat, targeting battery management systems through infected software updates, compromised USB devices, or network infiltration. Ransomware attacks specifically target energy infrastructure, encrypting critical system data and demanding payment for restoration.
Unauthorised access attempts frequently target weak authentication systems and default passwords on IoT devices. Cybercriminals exploit poorly configured access controls to gain administrative privileges, allowing them to manipulate system settings, steal sensitive data, or disrupt operations.
Man-in-the-middle attacks intercept communications between battery systems and monitoring platforms. These attacks can alter command signals, manipulate data readings, or inject malicious code into system communications. The wireless nature of many monitoring systems makes them particularly susceptible to these interception techniques.
Firmware manipulation targets the core software controlling battery operations. Attackers may install modified firmware to create backdoors, alter safety protocols, or establish persistent access to systems. This type of attack is particularly dangerous as it can remain undetected for extended periods while providing ongoing system access.
Data breaches targeting energy consumption patterns, operational data, and system configurations can provide valuable intelligence for future attacks or competitive espionage. The aggregated data from multiple battery installations can reveal broader grid vulnerabilities and operational patterns.
How can cyber attacks on battery storage systems impact your business operations?
Cyber attacks can trigger immediate system shutdowns and operational disruptions that halt energy production, interrupt power supply, and force manual intervention. These disruptions can cascade through your entire operation, affecting dependent systems and creating significant downtime costs.
Financial losses extend beyond immediate operational impacts to include recovery costs, system replacement expenses, and potential regulatory fines. Energy storage systems supporting critical infrastructure may face substantial penalty costs when service level agreements are breached due to cyber incidents.
Data theft compromises sensitive operational information, customer data, and proprietary system configurations. This information can be sold to competitors, used for industrial espionage, or leveraged for future attacks against your infrastructure or clients.
Safety hazards emerge when cyber attacks compromise battery management systems’ safety protocols. Manipulated charging cycles, disabled thermal management, or altered voltage controls can create fire risks, equipment damage, or personnel safety threats. These safety incidents can result in serious injuries and significant liability exposure.
Grid stability impacts occur when compromised battery systems fail to provide expected frequency regulation, load balancing, or emergency backup services. Large-scale battery installations play crucial roles in grid operations, and their compromise can affect broader energy network stability.
Regulatory compliance issues arise when cyber incidents expose inadequate security measures or data protection failures. Energy sector regulations increasingly require robust cybersecurity practices, and non-compliance can result in substantial fines and operational restrictions.
What security measures should you implement to protect connected battery storage systems?
Network segmentation isolates battery management systems from corporate networks and internet access, creating secure operational zones. Implement firewalls, VPNs, and air-gapped networks where possible to limit attack vectors and contain potential breaches.
Robust authentication controls include multi-factor authentication for all system access, regular password updates, and role-based access permissions. Replace default passwords immediately and implement strong password policies across all connected devices and management interfaces.
Encryption protocols protect data transmission between system components and monitoring platforms. Use industry-standard encryption for all communications, including wireless connections, cloud interfaces, and remote monitoring systems. Ensure encryption keys are regularly updated and securely managed.
Regular security updates and patch management keep system firmware, software, and security protocols current. Establish automated update procedures where possible and maintain detailed inventories of all connected devices requiring security maintenance.
Continuous monitoring systems detect unusual activity, unauthorised access attempts, and system anomalies in real-time. Implement security information and event management (SIEM) systems that can correlate data across multiple system components and trigger immediate alerts for suspicious activity.
Incident response planning prepares your organisation for rapid response to cyber threats. Develop detailed procedures for isolating compromised systems, notifying relevant authorities, and restoring operations safely. Regular testing and staff training ensure response plans remain effective.
Employee training programmes educate staff about cybersecurity risks, social engineering tactics, and proper security procedures. Human error remains a significant vulnerability, making comprehensive security awareness training an important component of your overall protection strategy.
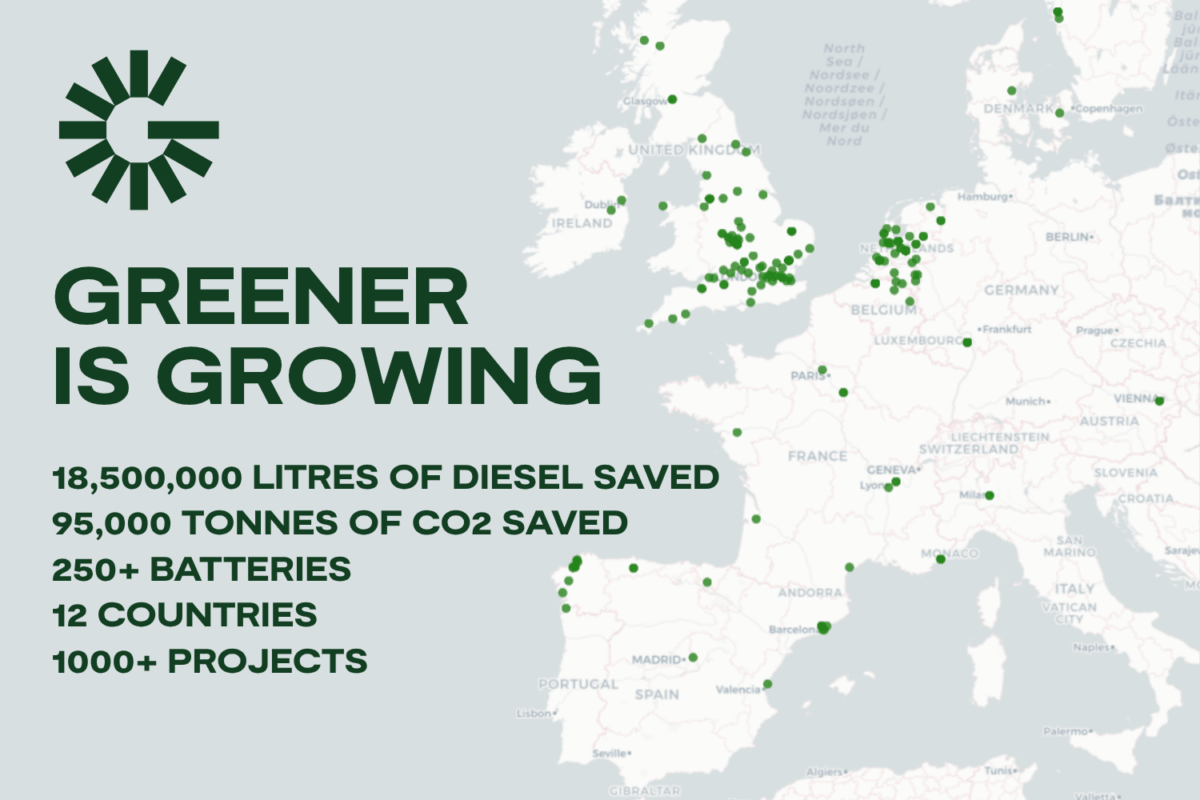
Understanding and addressing cybersecurity risks for connected battery storage systems requires comprehensive planning and ongoing vigilance. The interconnected nature of modern energy storage creates multiple vulnerability points that demand layered security approaches. By implementing robust security measures, maintaining current threat awareness, and developing strong incident response capabilities, you can protect your energy infrastructure while maintaining the operational benefits of connected systems. At Greener Power Solutions, we integrate security considerations into every aspect of our energy storage system design and implementation consulting, helping you build resilient and secure renewable energy infrastructure. Contact our expert team for comprehensive cybersecurity guidance tailored to your specific energy storage requirements.